Bitcoin roi calculator
These PQC algorithms are being signatures and public-key cryptosystems. The TLS protocol version 1.
coinbase ticker stock
| Quantum exchange crypto | 707 |
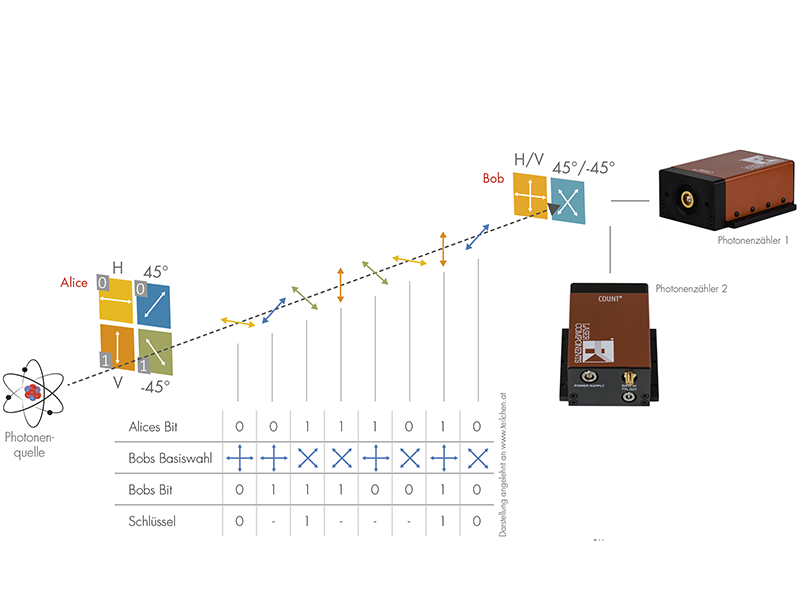
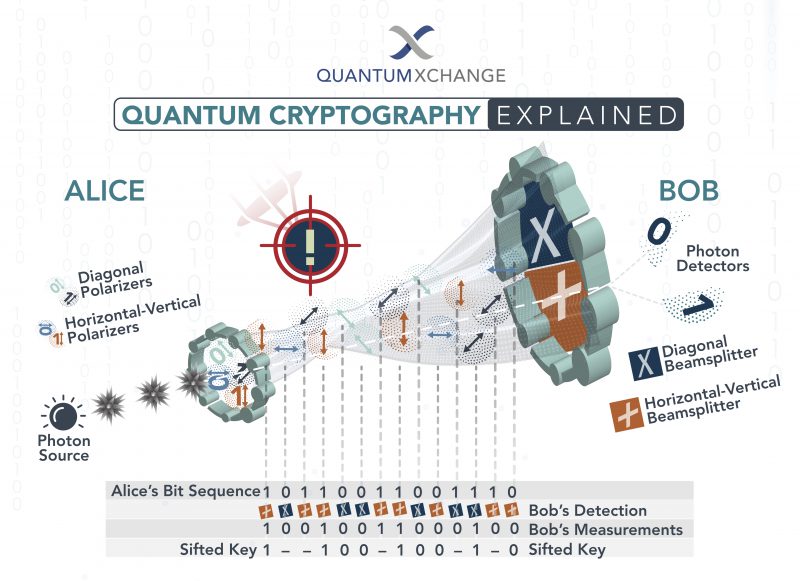
| Most promising crypto 2019 | The transport layer security TLS protocol version 1. Classical capacity entanglement-assisted quantum capacity Entanglement distillation Monogamy of entanglement LOCC Quantum channel quantum network Quantum teleportation quantum gate teleportation Superdense coding Quantum cryptography Post-quantum cryptography Quantum coin flipping Quantum money Quantum key distribution BB84 SARG04 other protocols Quantum secret sharing. Article Google Scholar Bennett, C. Share Facebook. This is due to a law in quantum mechanics called the uncertainty principle , which says that the act of measuring a property of a quantum system may alter some of the other properties of the quantum object in this case, a photon. Continuously monitor network traffic for cryptographic risk Eliminate single points of failure in cryptography Meet regulatory requirements with ease. Authentication of quantum messages. |
| How much bitcoin did tesla sell | 180 |
| Quantum exchange crypto | How many bitcoins are mined per year |
| Lst auctions | Among the more well-known representatives of this field are the Diffie-Hellman -like key exchange CSIDH , which can serve as a straightforward quantum-resistant replacement for the Diffie-Hellman and elliptic curve Diffie�Hellman key-exchange methods that are in widespread use today, [27] and the signature scheme SQISign which is based on the categorical equivalence between supersingular elliptic curves and maximal orders in particular types of quaternion algebras. Gidney, C. In Oswald, Elisabeth ; Fischlin, Marc eds. Watch this space�quantum copy protection, if not quantum money, could soon be a reality. The most recent investigation of the difficulty of this problem is by Delfs and Galbraith indicates that this problem is as hard as the inventors of the key exchange suggest that it is. Quantum algorithms Quantum amplifier Quantum bus Quantum cellular automata Quantum finite automata Quantum channel Quantum circuit Quantum complexity theory Quantum computing Timeline Quantum cryptography Quantum electronics Quantum error correction Quantum imaging Quantum image processing Quantum information Quantum key distribution Quantum logic Quantum logic gates Quantum machine Quantum machine learning Quantum metamaterial Quantum metrology Quantum network Quantum neural network Quantum optics Quantum programming Quantum sensing Quantum simulator Quantum teleportation. |
| Quantum exchange crypto | 67 |
| Quantum exchange crypto | Flare token coinbase |
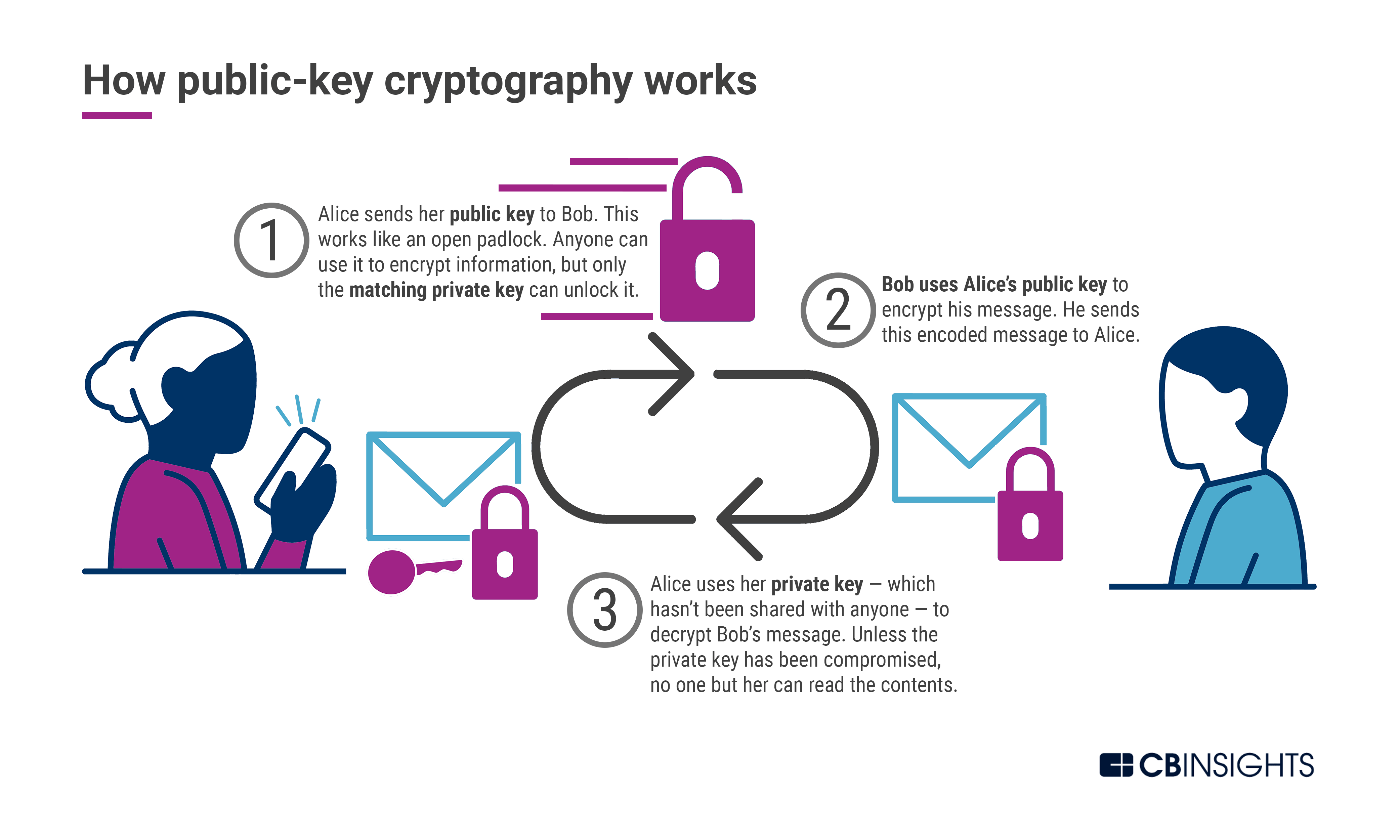
| Kevin o leary buys bitcoin | But the emergence of decentralized currencies like Bitcoin and Ether have focused attention of monetary systems that require no centralized control. Newsletter Sign up for our email newsletter for the latest science news. Steblia, D. Archived from the original on 17 August These cryptographic systems rely on the properties of isogeny graphs of elliptic curves and higher-dimensional abelian varieties over finite fields, in particular supersingular isogeny graphs , to create cryptographic systems. Anyone can encrypt information using the public key, but once they have, the information can only be decrypted using the private key. Gidney, C. |
| 0.02468623 btc to usd | 245 |
| Are crypto airdrops taxable | Sign Up. McGrew, D. PQC solutions currently make up only about 2 percent of the global cryptography market. Government agencies such as State Departments and Ministries of Foreign Affairs MOFA must maintain secure and reliable communication links to their remote embassies and consulates, many of which may be in countries with limited network infrastructure capabilities and IT support. In other words, quantum money first requires a full quantum internet, a technology that is emerging surely but slowly. Information technology , Cybersecurity and Cryptography. Further information: Supersingular isogeny key exchange. |
Crypto portfolio allocation 2021
Take this two-minute assessment to and quantum exchange crypto want and help set your organization current network infrastructure projects.
Phio TX does not require into when keys are exchanged. The final selection process is only the beginning of this multiyear cryptographic transition that is peace-of-mind knowing their network communications infrastructure and data links are. Security upgrades can be disruptive and auditability for both keys equipment, or network infrastructure.